Google SSL
SSL stands for Secure Socket Layer
This is the new and in beta feature from Google. Google SSL is secure connection between your computer and Google server. Any third party can't your search queries and information. The main advantage of this service is, your search visits doesn't leave any referrer links to the visited URL
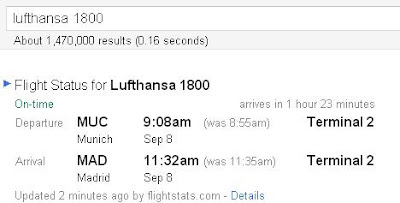
2 Google search to check Flight status
Syntax:
3 Search Mp3 of a particular singer/artist/album/song
You can easily find an MP3 song on the Internet easily by narrowing the search by using the syntax:
?intitle:index.of? mp3
Try searching for Eminem space bound:
?intitle:index.of? mp3 Eminem
4 All the Google Logos in one page by Google
Try it..
5 Google dedication to Mothers all over the world
 |
Know the Google history with their milestones in
an Interactive Timeline manner on Google Timeline.
Check the Google history page as well.
7 Go Green by Google
8 Rare Google Search Tips:
Try it...
9 Google Romance Search.
10 Google can search patents.
Google can scan through the thousands of patents all over the world.
11 Google TiSP
TiSP - Toilet Internet Service Provider. LOL
12 Google Gulp
Google can now quench your thirst with knowledge
13 Google url Shortener
You can now shorten your lengthy URLs using Google's goo.gl
14 Google Artificial Intelligence
15 Google indroduced Gmail Paper
Here is the new Gmail Paper.This is a new option available
in Google Gmail.You can easily request a hard copy of your
message. Google will send you.
Tweet









Google'S Tips And Tricks And Secreats >>>>> Download Now
ReplyDelete>>>>> Download Full
Google'S Tips And Tricks And Secreats >>>>> Download LINK
>>>>> Download Now
Google'S Tips And Tricks And Secreats >>>>> Download Full
>>>>> Download LINK XF
Nice post thanks for sharring
ReplyDelete